Опубліковано: 2026-05-02
The Math of Entropy: Why 12 Characters is Minimum
Password entropy explained with real math: H = L × log₂(R), RTX 4090 crack-time benchmarks, and why 12 characters is the floor — not the goal.
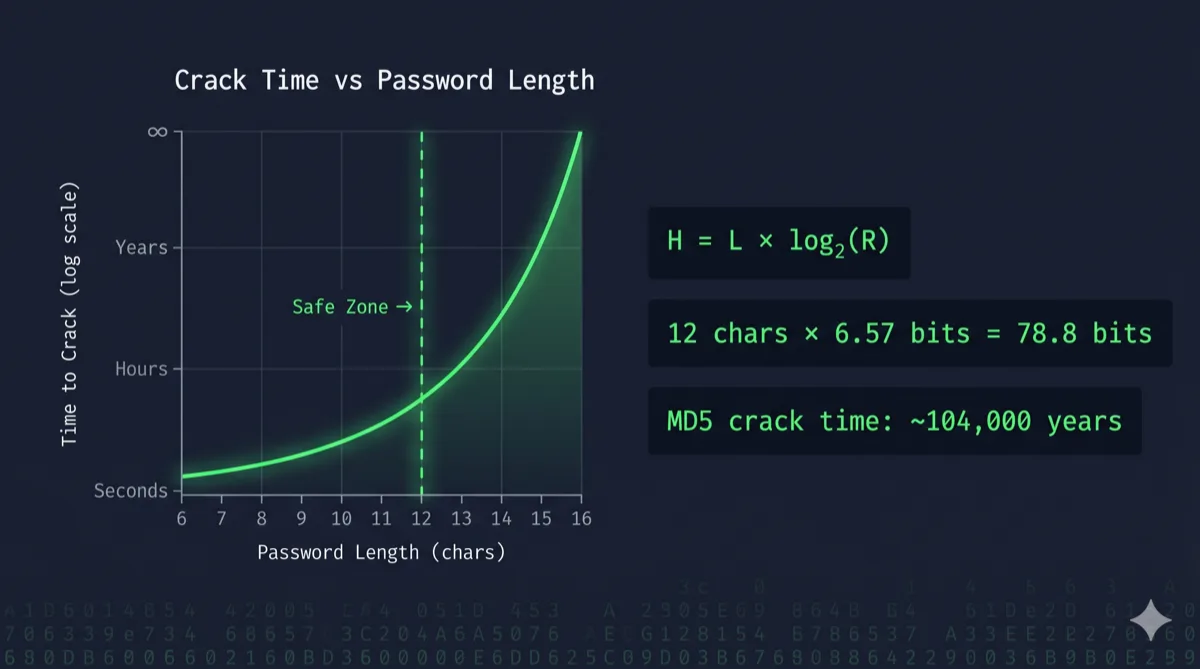
The minimum safe password length in 2026 is 12 characters — but only if you use the full character set. Use lowercase letters only and 12 characters buys you roughly 56 bits of entropy. That falls to a 7-day offline crack on a single RTX 4090. The formula is simple: entropy = length × log₂(charset size). Everything else follows from there.
This isn't a gut-feel recommendation. It's a direct consequence of attacker hardware costs dropping by half every few years while GPU parallelism keeps scaling. Let's do the math.
What is Password Entropy?
Entropy, in the information-theoretic sense, measures how many bits it would take to uniquely represent a value drawn from a given pool. For passwords:
H = L × log₂(R)
Where:
- H = entropy in bits
- L = password length (number of characters)
- R = size of the character pool (charset size)
A password with 80 bits of entropy requires an attacker to make up to 2^80 guesses to exhaust all possibilities. That's roughly 1.2 × 10^24 guesses. Even at 164 billion MD5 hashes per second on an RTX 4090, that's over 230 million years.
The key insight: every additional character multiplies the search space by R. Every additional symbol type multiplies each position's contribution by log₂(R_new / R_old). Length wins. Always.
Charset Size: The log₂(R) Multiplier
Here's how much entropy each character pool contributes per character:
| Character Set | Pool Size (R) | Bits per Character |
|---|---|---|
| Digits only (0–9) | 10 | 3.32 |
| Lowercase letters (a–z) | 26 | 4.70 |
| Lowercase + digits | 36 | 5.17 |
| Mixed case (a–z, A–Z) | 52 | 5.70 |
| Mixed case + digits | 62 | 5.95 |
| Full printable ASCII | 95 | 6.57 |
The jump from digits-only to full ASCII is 3.25 extra bits per character. Significant — but not as significant as people think. Adding one character to a full-ASCII password adds 6.57 bits. Switching from digits to symbols adds ~3.25 bits per character total. For a 12-character password, one extra character outperforms adding a symbol class.
This is why "add a special character" is a weaker rule than "make it longer."
The 12-Character Floor: What the Numbers Say
Entropy math is only useful if you benchmark it against real attacker hardware. Here's what a single RTX 4090 can do in 2026:
- MD5: ~164 billion guesses/sec
- SHA-256: ~23 billion guesses/sec
- bcrypt (cost 10): ~184,000 guesses/sec
- Argon2id: ~15,000 guesses/sec
Now plug those into the search-space formula. The table below shows worst-case exhaustion times (average is roughly half):
| Password | Charset | Entropy | MD5 Exhaust Time | bcrypt Exhaust Time |
|---|---|---|---|---|
| 8 chars, lowercase | 26 | 37.6 bits | < 2 seconds | 13 days |
| 8 chars, alphanumeric | 36 | 41.4 bits | ~7 seconds | 87 days |
| 8 chars, full ASCII | 95 | 52.6 bits | 11.2 hours | ~1 year |
| 10 chars, full ASCII | 95 | 65.7 bits | 11.6 years | 10.3 million years |
| 12 chars, full ASCII | 95 | 78.8 bits | ~104,000 years | 93 billion years |
| 16 chars, full ASCII | 95 | 105.1 bits | beyond heat death | beyond heat death |
The inflection point is clear. At 12 characters with full charset, you're at ~79 bits of entropy. Even against raw MD5 — the weakest stored-password scenario you'd encounter in the wild — the crack time exceeds the age of the universe.
Below 12 characters with full charset, you start taking on real risk. An 8-character full-ASCII password cracks in under half a day against MD5. That's not theoretical. Credential databases from breaches are cracked offline, at scale, every week.
The Hash Algorithm Multiplier
The tables above assume an attacker knows what hash function was used. That's the offline attack model: your credentials were leaked in a breach, the attacker has the hash file, and they're running it locally on GPUs they own.
If the site used MD5 or unsalted SHA-1, your 8-character password is gone in hours. Those hash functions were never designed for password storage — they're optimized for speed.
If the site used bcrypt, scrypt, or Argon2id, even a weak password gets a significant multiplier. bcrypt at cost 10 throttles attacks to ~184,000 hashes/sec. Argon2id drops that to ~15,000. Your 8-character lowercase password that dies in 2 seconds against MD5 survives 13 days against bcrypt. Still not safe. But the difference is instructive.
The problem: you don't control how services store your password. You don't know if that startup you signed up for three years ago hashed with MD5 or bcrypt. You must assume worst-case. Design your passwords around MD5 speeds. Everything else is a bonus.
Entropy Is Not Strength
One important distinction: entropy measures randomness, not memorability patterns. A password like Password1! has the characters to score well on naive strength meters — uppercase, lowercase, digit, symbol. Its actual entropy against dictionary + rule-based attacks is near zero. It's in every wordlist, with every common substitution pattern pre-applied.
Entropy math assumes your password was drawn uniformly at random from the full character pool. If you generated it yourself, under time pressure, trying to satisfy a strength policy, it wasn't. Your brain is a terrible CSPRNG.
This is why generation matters as much as the formula. A 12-character password only achieves its theoretical entropy if the generation source is cryptographically unpredictable.
Avoid tools that use Math.random(). Our Password Generator uses the Web Crypto API (crypto.getRandomValues()), ensuring your entropy source is as secure as your operating system's kernel.
Measuring Your Password's Actual Entropy
You don't have to run the math by hand. Our Password Strength Checker — Zero-Knowledge, runs 100% in your browser's volatile memory, nothing transmitted to any server — calculates entropy bits, estimates crack time against MD5 and bcrypt, and rates your password's strength against 2026 GPU benchmarks.
Paste a password in. You'll see entropy in bits immediately. If it's under 60, replace it. If it's under 80, at minimum ensure the site uses bcrypt. If it's 80+, you're operating above the safe threshold for current hardware.
One important caveat: entropy math protects against brute-force. It's powerless if a service leaks your password in plaintext. If you've been in a breach, a high-entropy replacement is step one — but there's a full triage workflow beyond that. See our guide to protecting your identity after a data breach.
🛡️ Security Checkpoint — Complete This Step
Most breached passwords were under 10 characters. Check your existing passwords and regenerate anything below the 12-character entropy floor.
- → Check your password entropy — instant bits calculation and crack-time estimate against MD5 and bcrypt
- → Generate a 16-character password — full ASCII charset, cryptographically random, zero server contact
- → Verify your own hashes — if you store or compare passwords yourself, use SHA-256 minimum
The Practical Takeaway
The math gives a clear answer. 12 characters with full ASCII charset puts you at 78.8 bits of entropy — above the threshold where current hardware becomes irrelevant regardless of hash algorithm. Below that threshold, your security margin depends entirely on how the receiving server stores your password. You can't control that.
The rule: minimum 12 characters, full character set, cryptographically generated. That's not a committee recommendation. It's what the numbers say.
For anything high-value — email, banking, password manager master password — use 16+ characters. That's 105+ bits of entropy. No realistic hardware configuration exhausts that in any plausible timeframe.
Frequently Asked Questions
How many bits of entropy is considered a strong password?
60+ bits is widely considered strong for most consumer accounts. 80+ bits is very strong — sufficient to resist offline brute-force against MD5 at current GPU speeds indefinitely. NIST SP 800-63B (Digital Identity Guidelines) recommends evaluating memorized secrets against attacker capability, explicitly flagging anything under 6 characters as unacceptable.
Below 40 bits is the danger zone. A 40-bit search space is exhausted in under 6 seconds at MD5 speeds on a single RTX 4090. If your password is under 8 characters with a small charset, it provides no meaningful protection against an offline attack.
Why is 12 characters the minimum password length?
It's the length at which a full-charset password crosses 78 bits of entropy — the point where offline attacks on common hash functions (MD5, SHA-256) exceed attacker ROI by orders of magnitude.
Below 12 characters with full ASCII, you start hitting crack times measured in hours or days rather than millennia. Above 12 characters with full ASCII, the search space grows fast enough that no realistic GPU cluster can exhaust it. 12 is the inflection point.
Does adding special characters help more than adding length?
No. Adding special characters expands the charset from 62 to 95 characters — a gain of log₂(95/62) ≈ 0.62 bits per character. For a 12-character password, that's about 7.4 total bits.
Adding one character at the same full-ASCII charset adds 6.57 bits — nearly the same gain from a single keystroke. For longer passwords, length gains compound faster. Add length first; special characters are a secondary multiplier.
What is the entropy of a random 8-character password?
At full ASCII (95 chars): 8 × log₂(95) ≈ 52.6 bits. That sounds reasonable until you benchmark it. At MD5 speeds (164 billion/sec on a single RTX 4090), exhaustion takes ~11.2 hours. A small GPU cluster cracks it in under an hour. Against bcrypt it survives about a year — but most legacy breach databases used MD5.
Is entropy the same as password strength?
Not exactly. Entropy measures the theoretical unpredictability of a randomly-generated password from a given charset. Password strength meters that check for dictionary words, patterns, and common substitutions are measuring something different — how easy the password is to guess using smart attacks rather than pure brute-force.
A password can have high theoretical entropy but low practical strength if it was human-chosen rather than randomly generated. Use a cryptographic generator, not your own creativity. The Password Generator is built specifically for this.